The Cloud technology is one of the trending business strategies used by various businesses in the present market. The cloud comes with various benefits like – all-time accessibility, cost-effective, higher flexibility and storage etc etc…and the list goes on.
What is Cloud Computing?
Cloud computing is an On-Demand availability of the computer system resources which offers IT as a service. You get the complete hosting facility from a dedicated cloud solutions provider without any bugs in working to store all your database. The cloud provider save all your data and protect them from any of the virus attacks, malfunctioning etc.
In a cloud computing system, the workload is handled by network of computers or the cloud system handles the load, and the end user computer load is reduced to minimal. The cloud interface is required for the client machines to connect to cloud system and all the applications are run on the cloud system. This reduces significant shift in the work load from client/end-user computers to cloud computers. Even the hardware and software requirement is reduced for the end user. Cloud computing can also be called as an internet based technology, provided as a service and on demand to the customers. The user can access the resources through the cloud provider over the internet as and when required.
Read our blog – What Is Cloud Computing?
Advantages of cloud computing
- Work flexibility
- Reduces IT costs
- Scalability
- Privacy and data security
- Easily accessible
- Modernised and upto date
- Easy sharing of data and information
- Automated software updates
- Reliable solution
Read our blog – Benefits of Cloud Computing
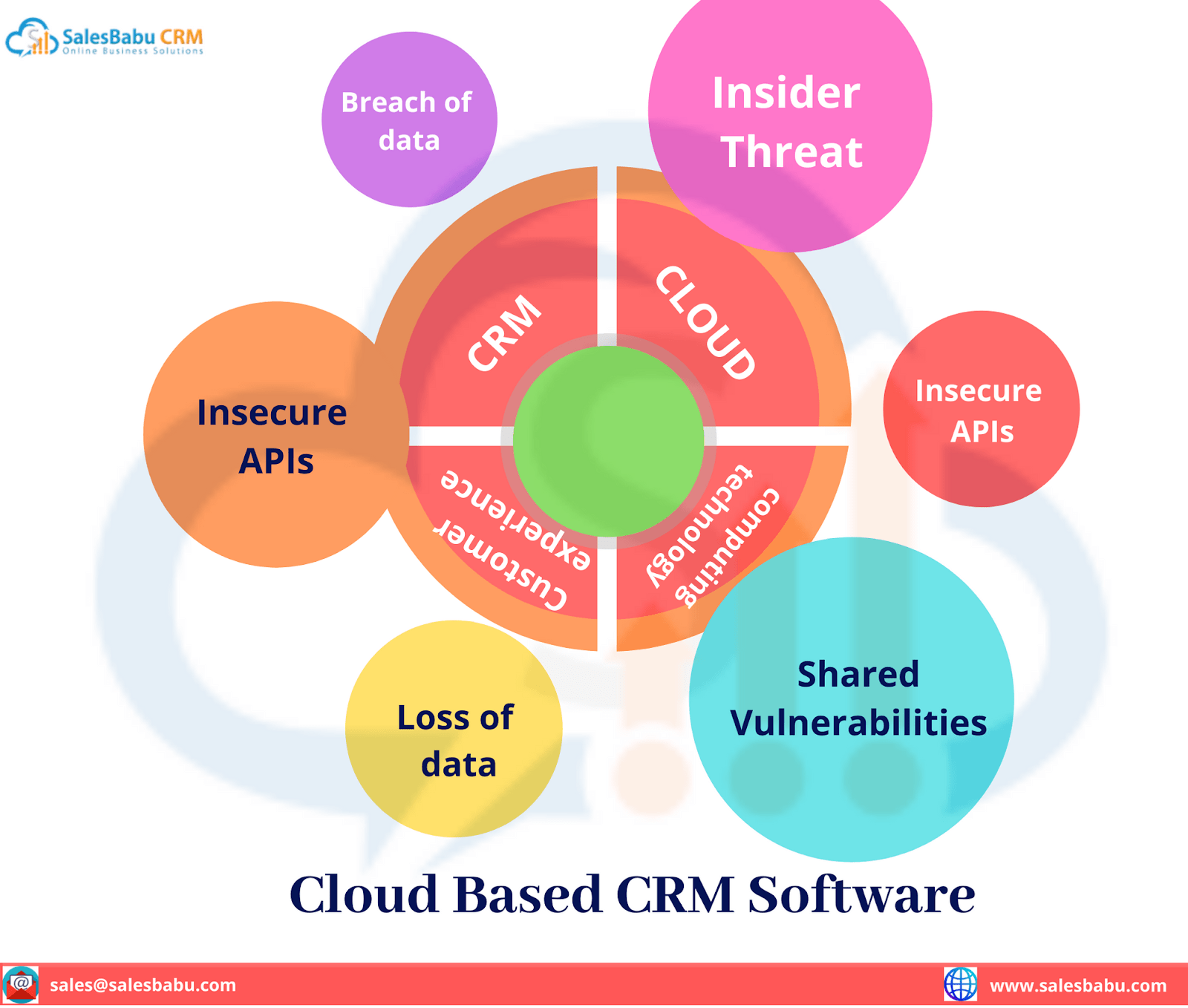
Though the cloud technology has multiple benefits, there are certain pitfalls with regard to security concerns which are stopping several companies from using the cloud computing systems. Here are a few cloud security concerns –
Cloud Security Considerations
1. Data Breach
Several companies implement cloud computing technology to reserve their comprehensive business details, creating cloud security an important component of entire security strategies. An information breach refers to a confirmed occurrence where hypersensitive, confidential, or protected information is disclosed or accessed through unauthorized means. Inefficient security practices or employees availing the cloud system via personal devices such as laptops or smartphones can uncover the system to vulnerabilities and with an objective to attacks, resulting in information breaches.
2. Insider Threat
The insider threat consists of a security risk emerging within the organization, typically from individuals with inside details, such as personnels or business associates. Insider threats may include the unauthorized leakage of confidential information. In cases where the cloud server is accountable for information security, the risk of insider threats is frequently heightened.
3. Insecure APIs
Web and cloud services uncover application programming interfaces (APIs) for third-party accessibility. Although, several developers and customers deficiently secure the keys to the cloud and their information. The API keys, when compromised, can result in denial of service or lead to the victim incurring fees if service providers are not watchful.
4. Shared Vulnerabilities
Shared susceptibility should not be dissolved lightly, as they can lead to information breaches and information loss. Shielding the cloud is a cooperative responsibility among the cloud service provider and the client (enterprise). The amount of responsibility allocated to each entity is based on the type of cloud service implemented by the enterprise.
5. Loss of Data
The loss of necessary business information possesses a significant risk to the organization. Information loss can happen because of accidental deletion, information overwriting, or malicious actions. Introducing robust cloud security measures is necessary to mitigate the risks connected with information loss.
6. Hijacking of Accounts
Attackers will have the ability to use your login details to remotely access the sensitive data that is stored in the cloud; additionally, attackers can forge and manipulate the information through hijacking credentials. Other methods of hijacking are reused passwords and scripting of the bug, which allows the attackers to easily and often without detection to steal credentials.
7. Denial of Service Attacks
Unlike the other kinds of cyberattacks which are generally launched to initiate a long-term foothold and hijack sensitive information, denial of the services assaults do not attempt to breach your security perimeter. Rather, they attempt to make all your servers and websites unavailable for authorized users. In some of the cases, however, the DoS is also used as the smokescreen for the other spiteful activities, and to take down all the security tools like web application firewalls.
8.Malware Injection
Malware injections are the code implanted or the scripts into cloud services that act as “valid instances” and run as SaaS to the cloud servers. This means that malevolent code can be injected into the cloud services and viewed as the part of a software or service which is running within the cloud servers by itself.
How to get over Cloud Security Concerns?
1. Breach of data
Here are certain steps to reduce the risk of data breaches –
- Verify the users accessing the network.
- Set access permission to users based on the applications and data required by them.
- Verify every software running on the computers.
- Monitor all network activities.
- Work with a trusted cloud vendor.
2. Insider threat
Insider threat can be avoided by –
- Controlled access
- Prioritizing initiatives
- Business partnerships
3. Insecure API
Here are certain steps to avoid access of API keys –
- Focus on designing APIs with adequate authentication
- Access control
- Encryption technology
4. Shared vulnerabilities
Here are certain tips to avoid shared vulnerabilities –
- Protect user password
- Access restriction to the device
- Multi-factor Authentication
5. Loss of data
Make use of a trusted cloud service provider to avoid loss of data as cloud ensures data backup.
Why switch to Cloud technology?
Switching to cloud technology can be beneficial to the business as it is a safe way of storing and managing data. It can turn out to be a valuable asset for your company because the cloud computing comes with a technology such as cloud storage, cloud backup and cloud hosting.
No matter if you are a small business or a start up, but when you stay organised and try to maintain consistency while growing, it is an effort worth contributing. Any business for that matter has loads of data to be stored depending upon the size of the business. You cannot just make use of the excel sheets and spend time on manual enterings. Whereas, with a cloud system can keep your work organised because the advantages of cloud computing helps in right management of the organisation.
Read our blog – Switch to Cloud Based CRM

Read our blog – 3 Reasons why CRM and Cloud computing is critical for your business growth?
Conclusion
Cloud system has definitely changed the dynamics of the IT Industry. The Cloud Computing has certainly proven to offer tremendous benefits to the business firms. Using Cloud Based CRM software in your business can make you lead ahead of the game in your industry. No matter if its an FMCG, pharmaceutical or a travel industry, ect, you can still keep yourself ahead of all. It not only comes with a cost effective plan but also makes your work easier and quicker.
SalesBabu Cloud Based CRM Software uses cloud computing technology. It provides the secured data storage on the cloud system. If you are looking for a cost effective CRM in cloud computing then contact the best CRM software and you can also request for a free CRM demo at https://www.salesbabu.com/.













